AI-Powered GRC
Compliance that scales intelligently with your business

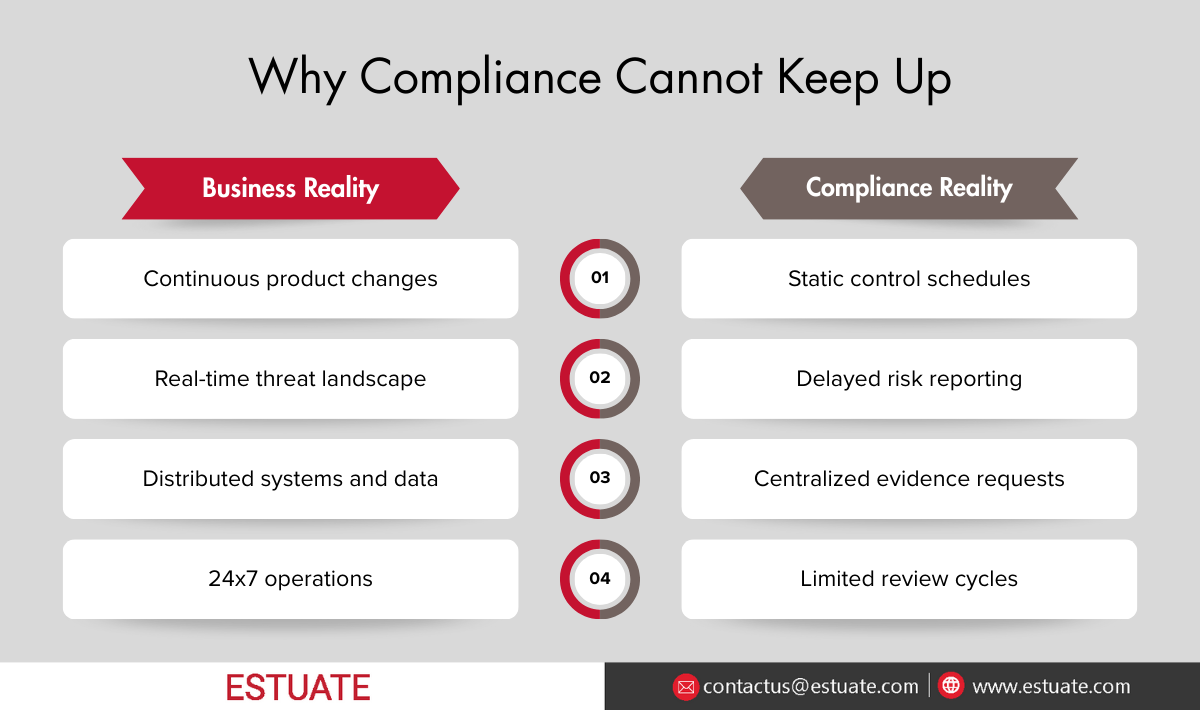
Most enterprises have modernized almost everything from customer systems to development pipelines to data platforms. Compliance is still trying to catch up.
The pressure is getting heavier each year.
A recent industry report shows that 85 percent of organizations say regulatory demands have become more complex in the last three years.
Yet only 29 percent report that their compliance programs consistently meet internal and external standards.
The strongest use cases focus on core outcomes:
- Reduce repetitive, manual effort
- Speed up decisions with better insights
- Deliver clarity or value that conventional tools cannot
The scale of work is also becoming unsustainable. Compliance teams collectively spend thousands of hours every year just managing workflows and documentation. Manual effort cannot keep up with the speed of modern business.
This is where AI becomes relevant. Not because it is trendy, but because compliance cannot scale without automation that continuously supports assurance.
The goal is not to make compliance futuristic. The goal is straightforward:
Compliance that moves as fast as the business.
Business speed increases automatically. Compliance speed increases only with effort.
“Compliance cannot scale through manual effort. It needs assurance that runs at business speed.”
Govern. Mitigate. Comply.
Build a structured GRC framework to ensure business continuity and regulatory adherence.
1) Why AI Matters in GRC
GRC teams are responsible for protecting the organization, yet much of their time is spent managing manual activities that repeat continuously. These activities are necessary, but they are not strategic. They involve collecting evidence, proving controls, preparing documents, tracking remediation tasks, and maintaining the same information across multiple frameworks.
As regulatory expectations continue to expand, these tasks scale faster than the workforce can keep up. Global research confirms this trend. Compliance costs rose by 15 percent in a single year for regulated enterprises, driven primarily by manual documentation and evidence management requirements.
Most time is spent collecting and repeating work, not evaluating risk.
The problem is not the number of controls or audits. The real challenge is that most of GRC operations still rely on:
- Periodic testing instead of continuous assurance
- Manual evidence uploads instead of data from source systems
- Framework duplication instead of reusable control mapping
- After-the-fact reporting instead of active monitoring
These practices slow down risk response and create a constant backlog of work that never truly decreases. AI creates value by addressing exactly these friction points.
Here is where AI becomes practical in GRC:
| GRC Activity | Traditional Effort | AI Value |
| Control Testing | Periodic, manual sampling | Continuous, full-population testing |
| Evidence Collection | Emails, uploads, screenshots | Automatic extraction from source systems |
| Risk Monitoring | After-the-fact reports | Real-time anomaly detection |
| Multi-Framework Compliance | Repeated work across standards | Control harmonization and reuse |
| Audit Preparation | Weeks of documentation | Ready-to-review evidence packages |
The value of AI is not limited to efficiency. It improves consistency, reduces repeated tasks, and removes delays that arise from manual coordination. AI makes it possible to scale compliance without scaling headcount at the same rate.
Most organizations do not need more GRC tools or new security dashboards. What they need is a way to make their existing governance processes less dependent on human effort. AI becomes effective when it supports the parts of GRC that require repetition, precision, and constant monitoring.
AI does not change governance requirements. It simply operates at a scale that people cannot manually sustain. Instead of teams collecting screenshots, sampling transactions, or waiting for quarterly assessments, AI works continuously in the background and produces evidence that is already mapped to controls.
A mature AI powered GRC model creates three operational shifts.
a) Evidence Is Generated, Not Collected
In most organizations, evidence is scattered across ticketing systems, identity platforms, cloud services, ERP data, CRM logs, and device records. GRC teams spend significant time asking for screenshots or duplicated exports.
An AI enabled approach extracts evidence directly from the systems where it lives. This removes coordination delays and greatly reduces the risk of missing or outdated evidence. It also ensures that what auditors receive is accurate and traceable back to source systems.
b) Assurance Becomes Continuous
Periodic testing was designed for a slower business environment. Products and services were not updated daily, and the attack surface did not change every week. Today, the pace is different.
Continuous testing supported by AI allows control assessments to run in the background, without manual scheduling. Instead of testing after a quarter, compliance validation happens within the same operational timeline as updates, deployments, and access changes.
c) Risk Is Visible Before It Becomes an Incident
Traditional GRC reviews often highlight issues after impact. This reactive approach limits the ability to prevent financial loss, compliance penalties, or customer impact.
AI powered GRC shifts the timing. Anomalies and deviations are flagged in real time, not after audits. This improves the organization’s ability to react to risk when it is still small, instead of reporting it after it has already caused disruption.
Together, these shifts deliver a measurable outcome: compliance becomes predictable instead of reactionary.
Modern GRC programs are no longer defined by documentation alone. They are defined by the ability to sustain assurance at business speed, with fewer manual touchpoints and greater accuracy.
AI shifts GRC from catch-up work to continuous assurance.
2) How AI Makes GRC Scalable Across Multiple Frameworks
For many organizations, the real workload in compliance does not come from the number of controls. It comes from maintaining the same or similar controls across several frameworks. A single access control may need to be validated separately under ISO 27001, SOC 2, HIPAA, PCI DSS, NIST or industry-specific regulations. The wording changes, but the intent remains the same.
This creates repetitive tasks across:
- Control definitions
- Evidence mapping
- Assessments and testing
- Audit documentation
The same control is explained, reviewed, and proven multiple times for different certifications. As more regulations evolve, these repetitions grow.
How AI Reduces Repetition Through Harmonization
AI can identify overlaps across frameworks and determine where a single control or evidence source can satisfy multiple standards. This helps organizations:
- Reduce duplicated documentation
- Reuse evidence intelligently
- Avoid repeating the same assessment effort
- Maintain consistency when regulations change
Harmonization allows GRC teams to build once and reuse many times, instead of treating every framework as a separate project.
3) Where Platforms Support This Approach
Several platforms now enable AI supported harmonization, and they offer value when used with well defined processes and source-based evidence. TrustMosaic is one example that applies AI to map overlapping controls and reuse mapped evidence where applicable. It helps teams replace repeated work with a single unified control set that supports multiple standards.
This kind of platform support becomes meaningful only when:
- Controls are clearly defined
- Evidence comes from actual systems, not uploads
- The organization expects continuous rather than one-time compliance
- Multiple standards apply across the enterprise
The objective is not to automate everything. It is to build a compliance foundation that scales as regulations increase.
Harmonization is not a shortcut. It is a prerequisite for sustainable compliance in regulated organizations.
4) Introducing AI Into GRC Without Disruption
AI in GRC should never start as a technology decision. Successful adoption comes from strengthening governance first and then using automation to support it. When leaders jump directly to tools, they risk automating gaps, replicating inconsistencies, or creating frameworks that cannot be defended during audits.
A responsible approach to AI powered GRC respects three principles.
“AI does not replace governance. It amplifies well-designed processes and makes them sustainable.”
a) Strengthen Governance Before Automating
AI is effective only when controls, evidence sources, and ownership models are well defined. If processes are unclear, automation accelerates mistakes. Leaders should confirm:
- Controls are documented clearly
- Evidence sources are identified
- Accountability is assigned to roles, not tools
- Change management procedures exist for updated controls
Automation should reinforce governance, not replace it.
b) Integrate With Existing Systems, Not Around Them
The value of AI in GRC depends on accuracy and traceability. Evidence must come directly from the systems where it resides, not from email attachments or manually exported files. Leaders should ensure AI supports:
- Evidence from applications, logs, and identity systems
- Visibility into the source of every record
- Traceable proof that matches audit expectations
GRC should not become another data silo. It should be an extension of enterprise systems.
c) Support People, Not Replace Them
GRC requires decisions, interpretation, and judgment. AI can perform continuous testing, find overlaps, and handle documentation, but it cannot decide if a risk is acceptable or if a control meets business objectives. Leaders should position AI as a support layer that:
- Frees teams from repetitive documentation
- Improves the quality of assessments
- Offers real time insights to inform decision making
- reduces fatigue so experts can focus on risk strategy
AI is most valuable when it elevates human expertise instead of substituting it.
Simplify. Secure. Sustain.
Elevate your governance, risk, and compliance strategy with expert solutions.
Let’s Talk!
Leadership Outcome: Sustainable Compliance, Not Faster Checklists
Introducing AI responsibly creates a compliance model that keeps pace with business changes without requiring constant increases in effort or staffing. The goal is not faster audits or automated reports. The goal is a program that can scale, adapt, and provide reliable assurance year after year.
AI becomes successful in GRC when leaders treat it not as a replacement for governance, but as a multiplier for well designed processes.
Assurance at the Speed of Business
AI powered GRC is not a technology upgrade. It is a shift in how organizations maintain assurance as business environments become faster, more distributed, and more regulated. Compliance can no longer rely on periodic testing, repeated evidence requests, and duplicated work across frameworks. These practices were built for a slower enterprise, not for modern operations.
When governance is strong, AI becomes a multiplier. It brings continuous visibility, reduces repetitive tasks, and makes compliance scalable without increasing manual effort. It allows teams to spend more time evaluating risks and strengthening controls instead of collecting screenshots or rewriting the same documentation for multiple standards.
The future of GRC is not defined by automation alone. It will be defined by programs that can adapt to changing regulations, reuse work intelligently, and maintain evidence directly from source systems. Organizations that take this direction now will maintain a strategic advantage. They will spend less time proving compliance and more time improving it.
A number of platforms and service providers contribute to this shift. Estuate, through its work with AI supported harmonization and source based evidence models, demonstrates how strong governance combined with selective automation leads to sustainable compliance. The lesson is clear: tools matter, but only when they amplify well designed processes.
AI will not replace governance or risk expertise. It will give both the stability and space they need to operate at the pace of modern business.
That is the real value of AI powered GRC: less repetition, clearer visibility, and assurance that grows with the enterprise instead of slowing it down.
Let’s Talk Compliance That Keeps Up with Your Business
If you’re ready for a GRC program that scales with your enterprise with continuous assurance, less manual work, and real-time risk visibility — reach out to Estuate.
Contact Estuate:
https://www.estuate.com/contact/
Use the contact form, or email contactus@estuate.com to schedule a demo or consultation.