Another Mega Data Breach. This Time It’s Quora

Quora says 100 million users hit by a malicious attack. Here are the facts.
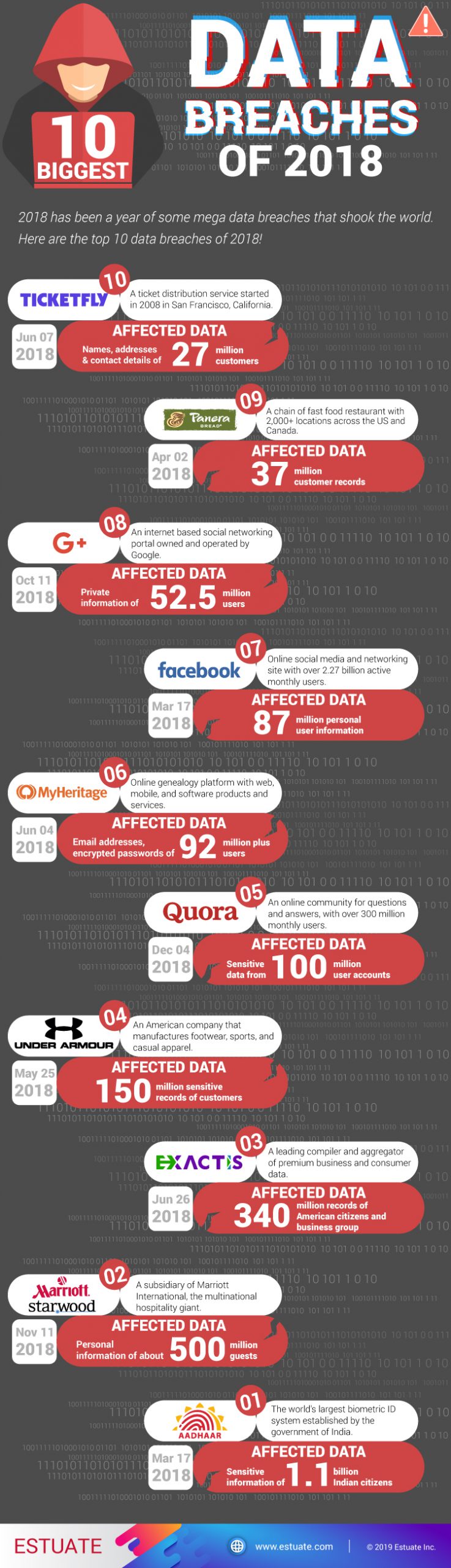
2018 was the year of massive technology advancements. From where we started this year to where we have come, the progress has been phenomenal. We saw some of the most breakthrough technology trends, such as Artificial Intelligence, Blockchain, Natural Language Processing and Internet of Things making it big in the business world. But at the same time, 2018 has also been a year of some of the most shocking and alarming cybercrimes.
Although the Facebook data breach made the most news, there were bigger cyber security incidents at several other top business houses including Panera, Under Armour and even Aadhar and Marriott International to name a few. These data breaches are believed to have compromised personal information of hundreds of millions of users and customers. And now, the hackers are back with a major data breach; this time at Quora.
Launched in 2010, Quora is an online community where people can post questions related to over 400,000 topics and get answers/advice from others. Over the years, Quora has grown to become the biggest online Q&A portal with at least 300 million monthly users and 300 million unique monthly visitors.
The company recently disclosed a mega data breach stating that nearly 100 million users were affected by unauthorized access to one of its systems by a malicious third party. The breach is said to have occurred on 30th November, 2018. Soon after the incident was confirmed, the Quora team notified its potentially affected users through an email.
“On Friday we discovered that some user data was compromised by a third party who gained unauthorized access to our systems. We’re still investigating the precise causes and in addition to the work being conducted by our internal security teams, we have retained a leading digital forensics and security firm to assist us. We have also notified law enforcement officials”, the email stated.
According to the initial investigation, the hackers could have possibly gained access to the following information.
-
Account and user information including name, email address, IP, user ID, encrypted password, user account settings, personalization data
-
Public actions and content including drafts, such as questions, answers, comments, blog posts, upvotes
-
Data imported from linked networks like contacts, demographic information, interests, access tokens
-
Non-public actions, such as answer requests, downvotes, thanks, etc.
“It is our responsibility to make sure things like this don’t happen, and we failed to meet that responsibility. We are continuing to work very hard to remedy the situation, and we hope over time to prove that we are worthy of your trust”, the email further stated.
Quora hasn’t disclosed any information about who the hackers might be. However, as an immediate corrective action, Quora invalidated the accounts of all the affected users and suggested them to reset their passwords.’
What does it teach us?
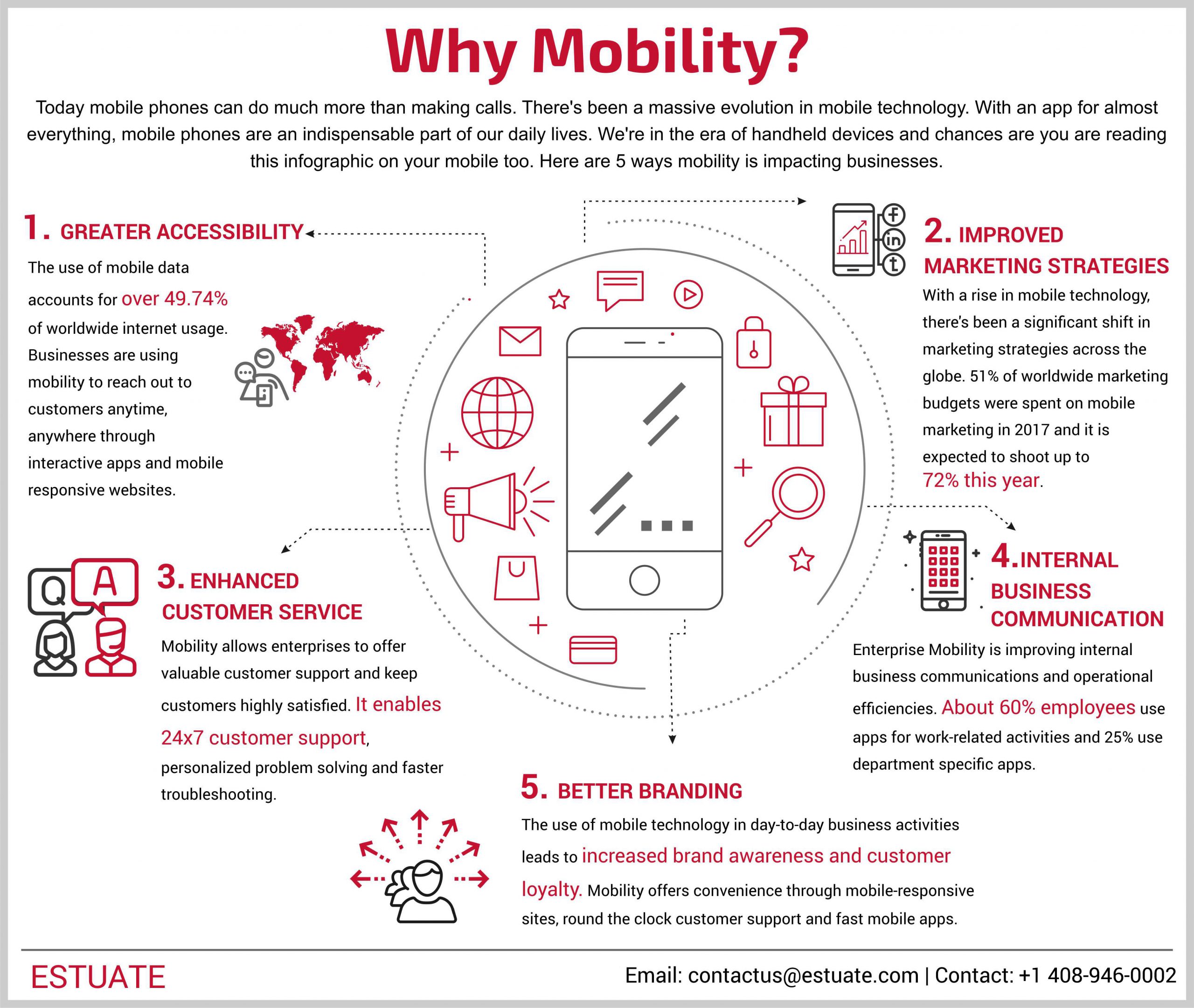
With each incident we’re reminded that we’re not completely secure. Every data breach is an alarm; a signal to never let your guard down. There are hidden lessons for us in every major data breach. They teach us that
-
Implementing modern technology comes with potential risks and these risks should be acknowledged with appropriate measures.
-
Cyber-attacks can have huge repercussions and can lead to major reputational loss. Building cyber resilience is not a good practice anymore, it is a must-have.
-
Insider threats and minor negligences can lead to huge information leakages; hence every data privacy practice must be followed with due diligence.
In conclusion, data breaches can occur anytime, anywhere, regardless of the information security measures we take. The best probable way to prevent cyber-crime or contain the impact of an attack at your enterprise is to keep your data privacy software updated, employ multi-layered, more reliable cybersecurity solutions and remain extra-vigilant, more than ever before!